This article looks at the possible privacy risks associated to Cloud computing and application permissions (consent to waive privacy rights) with reference to the right to data privacy. It also gives a brief overview of the international protection of the right to privacy and the current international movement to protect private data from governments to gauge how important the right to privacy is viewed. This is however not a legal article. I ask for common sense when you download Applications (Apps) and to educate yourself as to what you agree to when you give permission to Apps and accept certain responsibility for your own private data.
Clouds
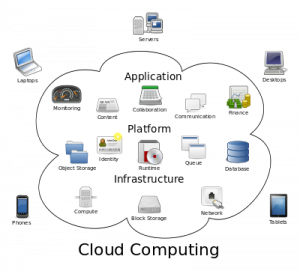
Cloud computing metaphor: For a user, the network elements representing the provider-rendered services are invisible, as if obscured by a cloud.
Cloud computing is an internet-based computing in which large groups of remote servers are networked to allow the centralized data storage, and online access to computer services or resources. Clouds can be classified as public, private or hybrid.
apps and privacy
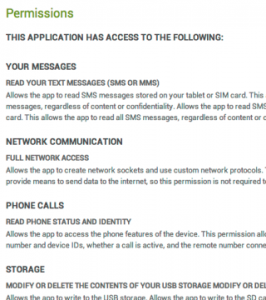
The first time I downloaded Apps from my Google Playstore on my Android I was concerned about the permissions that certain Apps require. The Apps were asking for consent to access my calls, sms’s, emails, location, among others. Certain Apps even has the ability to delete the data from my SD card (which had also happened in June 2014).[1]
our companion the mobile: permissions you give to Apps regarding your private information
In order to download Apps on your phone each Android user must give certain permissions to the App owner. This is probably the same for Apple, although I don’t use one. All major database Mega companies appear to be affected. See an article surrounding a recent leak of information on iCloud http://bgr.com/2014/09/21/apple-icloud-nude-photos-leak/).
WhatsApp and Facebook state the following about the reason for permissions. Almost all Apps need certain permissions to run on Android, and we use these permissions to help enable features in the App and create a better experience for you. Keep in mind that Android controls the way the permissions are named, and the way they’re named does not necessarily reflect how the Apps use them.
Android permission (what you’ll see on your Android phone or tablet) and examples of what we use this permission for includes:
- Take pictures and videos: This permission allows you to take photos and videos within the Messenger app to easily send to your friends and other contacts.
- Record audio: This permission allows you to record and send videos and voice messages and make voice calls within Messenger.
- Read your contacts: This permission allows you to add your phone contacts as Messenger contacts if you choose to do so. You can always stop syncing your phone contacts by going to your Messenger settings.
- Directly call phone numbers: This permission allows you to call a Messenger contact by tapping on the person’s phone number directly from the menu of your conversation with them.
- Receive text messages (SMS): If you add a phone number to Messenger, this allows us to confirm your phone number by finding the confirmation code that we send via text message.
With other words permissions are given for the App to work on the mobile’s platform (Android or Apple or Ubuntu…). So clearly you and I are not giving permission for our private data to be used by third parties.
The Physical Internet
When you’re on a Google website, you’re accessing one of the most powerful server networks in the known Universe…according to Google anyway. Google calls it the physical Internet.
Google’s Council Bluffs data center provides over 115,000 square feet of space. This is where you serve the internet in Google terms.
As part of their commitment to keeping the company’s users’ data safe they destroy all failed drives, on site. 
The website information is beautiful gives an illustration of the enormity of the problem. It illustrates by way of graphs how all the major data leakages took place and he type of information that was stolen, hacked, leased by error etc. Have a look at their site http://www.informationisbeautiful.net/visualizations/worlds-biggest-data-breaches-hacks/.
Do you ever think that your data privacy is maybe your responsibility? or the consequences of permissions you give to Google, Apple, Facebook, WhatsApp, Microsoft or the now commonly used Cloud, Dropbox? Are you a totally ignorant user.
Maybe it’s time you rethink your mobile use and data storage as indications are it’s no longer private and enforcing your rights are difficult if not nearly impossible across jurisdictions. As will be seen the current international and domestic protection to the right to data privacy is not sufficient to handle the mere enormity of its user base.
Privacy
In general the law provides that consent to disclosure of private facts or intrusion into the private sphere may be given expressly or impliedly. The consent must be given voluntarily and must be informed. Consent to disclosure given for a particular purpose may not be valid for disclosure for another purpose.
This is the central reason for the uproar seen on an international scale by Google and Microsoft (discussed below). These companies are legally at risk to class action claims for damages as user are normally not consenting to the sharing of their private data information with third parties including governments. Although certain governments agencies may legally get access to private data in performance of their functions (investigating a crime etc) privacy information may not be abused and third parties may not get arbitrary access.
This is what is happening in worrying scale. Although we give permission to data use for Apps to work our private information can be accessed and used for a different purpose such as intelligence or monitoring. There may be justified grounds for intelligence purposes, however even this aspect requires justifiable purpose must follow a judicial process.
international law protection of data privacy rights
The modern privacy benchmark at an international law level is found in the 1948 Universal Declaration of Human Rights, which specifically protects territorial and communications privacy.[2] Article 12 provides no one shall be subjected to arbitrary interference with his privacy, family, home or correspondence, nor to attacks upon his honour and reputation. Everyone has the right to the protection of the law against such interference or attacks.[3]
According to Jonathan Burchell, the word ‘arbitrary‘ points towards some acceptance that certain invasions of privacy may be regarded as reasonable and others as unreasonable. In fact, the Universal Declaration recognises limits to the exercise of rights. These limits are defined as those ‘determined by law solely for the purpose of securing due recognition and respect for the rights and freedoms of others and of meeting the just requirements of morality, public order and the general welfare in a democratic society’. ( Article 29).
The right to privacy is also dealt with in various other international instruments, such as the United Nations Convention on the Rights of the Child, the International Covenant on Civil and Political Rights (ICCPR), and the United Nations Convention on Migrant Workers. On a regional level, a number of treaties make this recognition of the right to privacy legally enforceable.
a) Article 8 of the European Convention for the Protection of Human Rights and Fundamental Freedoms 1950 states: (1) Everyone has the right to respect for his private and family life, his home and his correspondence.
There shall be no interference by a public authority with the exercise of this right except as in accordance with the law and is necessary in a democratic society in the interests of national security, public safety or the economic well-being of the country, for the prevention of disorder or crime, for the protection of health of morals, or for the protection of the rights and freedoms of others.
b) The American Convention on Human Rights (Art 11,14) and the American Declaration on Rights and Duties of Mankind (Art V,IX and X) contain provisions similar to those in the Universal Declaration and International Covenant. The African Charter on Human and People’s Rights does not make any reference to privacy rights. This should probably be amended.
There is movement by international organisations to put mechanisms in place to protect data privacy. The International Organisation of Standardization has recently published standards for the protection of privacy data.[4] These standard will form the basis for the protection of data privacy. But there is still no universal implementation of these standards and we have no idea of the extent of privacy of our data.
Burchell submits that privacy is most often seen as a fundamental personality right deserving protection either as part of human dignity or, if not subsumed under dignity, nevertheless warranting independent, but similar, protection to other facets of personality rights like dignity or reputation. The argument for recognizing privacy is an independent right really only acquires significance where the concept of impairment of dignity is given a narrow focus, linked to insulting behaviour. If however, dignity is given its true human rights sweep, ranging beyond mere prevention of insulting conduct, then privacy can rightly find its place as part of the fundamental right to human dignity. Aspects of individual autonomy are more appropriately located within his broad concept of ‘dignity’ than under an artificially extended concept of ‘privacy’, as in the United States of America.[5]
south african protection of privacy rights
In South African law the general defences to an action for invasion of privacy, or grounds of justification, are public benefit (interest) and consent.[6]
As fault in the form of intention is required for the liability of an individual for invading another’s privacy and negligence might be sufficient for the liability of the media for invasions of privacy, then absence of fault on the part of a defendant will also be a defence.
For instance, if an individual genuinely believed that consent to disclosure of information had been given, then intention (or, as it is called in South Africa, animus iniuriandi) would be lacking. If negligence is regarded as sufficient for the liability of the media for invasions of privacy, and there is some recent judicial support for this approach, then a journalist who has taken reasonable steps to verify that consent has been given will have a defence of absence of negligence.
The Protection of Personal Information Act 2013 (POPI)
Personal Information broadly means any information relating to an identifiable, living natural person or juristic person (companies, CC’s etc.) and includes, but is not limited to:
- contact details: email, telephone, address etc.
- demographic information: age, sex, race, birth date, ethnicity etc.
- history: employment, financial, educational, criminal, medical history
- biometric information: blood type etc.
- opinions of and about the person
- private correspondence etc.
Processing means broadly anything done with the Personal Information, including collection, usage, storage, dissemination, modification or destruction (whether such processing is automated or not).
Some of the obligations under POPI are to:
- only collect information that you need for a specific purpose
- apply reasonable security measures to protect it
- ensure it is relevant and up to date
- only hold as much as you need, and only for as long as you need it
- allow the subject of the information to see it upon request
Although POPI makes provision for a Information Regulator its not operational yet. We have no indication how the Information Regulator will manage the da theft in other jurisdictions although some protection is provided in Section 72 of POPI.
alleged infringement of data privacy – the right to know when private information is shared with governments.
According the UK Guardian, Yahoo was threatened with a fine of $250 000 a day if Yahoo failed to provide data to the US government agencies.[7]
Microsoft and Google have decided to sue the US Government over claims that it is illegally stifling the release of more details about communications surveillance activities in the country. Both companies were named in documents leaked from the US National Security Agency (NSA) and published in a number of newspapers, including the Guardian in the UK, in connection with the operation of a computer system called ‘Prism‘ by the Russian refugee John Snowden. The documents claimed that officials at the NSA could use Prism to access information stored by Microsoft, Google, Facebook and a number of other technology companies for surveillance purposes.
On 2 June 2014, a Mr Elliott J. Schuchardt, instituted a lawsuit filed against President Barack Obama, James R. Clapper, as Director of National Intelligence, Admiral Michael R. Rogers, as Director of the NSA, James B. Comey, as Director of the FBI, in the United States District Court for the Western District of Pennsylvania. The case contends that the Defendants are violating the Fourth Amendment of the United States by collecting the full content of e-mail in the United States (and probably us all). The complaint asks the Court to find the Defendants’ program unconstitutional, and seeks an injunction.
The US public are also fighting the arbitrary access to private data. Two class actions by the American Civil Liberties Union (ACLU) and FreedomWatch USA (FWUSA) was instituted. The lawsuit by ACLU was filed against the NSA citing that the “Mass Call Tracking Program” (or PRISM) “violates Americans’ constitutional rights of free speech, association, and privacy” and constitutes “dragnet” surveillance, in violation of the First and Fourth Amendments to the Constitution, and thereby also exceeds the authority granted by 50 U.S.C. § 1861, and thereby violates 5 U.S.C. § 706. The case was joined by Yale Law School, on behalf of its Media Freedom and Information Access Clinic.
FWUSA is suing government bodies and officials believed responsible for PRISM, and 12 companies (including Apple, Microsoft, Google, Facebook, and Skype and their chief executives) who have been disclosed as providing or making available mass information about their users’ communications and data to the NSA under the PRISM program or related programs. The case cites the First, Fourth, and Fifth Amendments to the Constitution, as well as breach of 18 U.S.C. §§2702 (disclosure of communications records), and asks the court to rule that the program operates outside its legal authority (s.215 of the Patriot Act). The class includes the plaintiffs “other American citizens who, in addition to being members of the Nationwide Class, had their telephone calls and/or emails and/or any other communications made or received through Facebook, Google, Yahoo, YouTube, Skype, AOL, Sprint, AT&T, Apple, Microsoft and/or PalTalk actually recorded and/or listened into by or on behalf of [the] Defendants.”
Microsoft and Google have pressed the US Government for permission to release more details about the surveillance activities that the data they collect is subject to. The companies have stressed previously that they do not grant direct access to their systems but that they do accede to legal requests for access to data they store.
Some technology companies, including Microsoft and Google, do publish some information about the data requests they receive. However, Microsoft has now announced that the two companies will press forward with legal action first initiated in June after failing to agree with the US Government about the extent of the details they can release, it said.
Amidst uproar from privacy groups following the Prism programme revelations, US government and intelligence officials claimed that the data accessed by the NSA is in line with the US’ Foreign Intelligence Surveillance Act (FISA).
FISA sets out the procedures that US intelligence agencies have to follow in order to gather foreign intelligence information about foreign based individuals for the purposes of protection against attacks on the US, such as terrorism. Under the regime intelligence agencies require a court to sanction the acquisition of data, although privacy groups have challenged the thoroughness of the procedure. [8]
Interim Solution
The website Life Hacker advises that the first thing is to understand what all of those permissions are that you agree to. Some Apps ask for tons just to work (Facebook, Google+, Gmail, etc) while others ask for relatively few. (This thread at Android Forums) does a great job of explaining how permissions work, and what each type does, complete with examples for what each permissions type means. It’s a good read, but ultimately it’s less important that you understand what each permissions type means as compared to that you understand why an App is requesting it when you install or update.
Make sure you read the list of permissions, and try to correlate each one back to some feature or function of the App. If you can reasonably tie an App’s permissions back to a feature (an SMS App that needs to read SMS messages, or a caller ID App that needs access to “read phone state and identity,” for example) then there’s little to worry about. Let’s face it, most of the time, the reason an App asks for the permissions is because it needs them to work.
The problem is while we do have the protection from violations of data privacy but its not really enforceable for the average individual. This should be your motivation to make your responsibility to ensure as much privacy as possible.Keep your emails on your computer not in the clouds, keep privacy information on an external etc.
Conclusions
It has been revealed to us that data we deem private is used by certain governments to monitor and use in the name of national security and the prevention of crime. We do not have control over these types of privacy infringements. I believe it is the service providers or the privacy data protectors who should take special measures to ensure that privacy is protected from abuse in this type of scenario.
You as a user of the internet-as-a-phone including the download of Apps and users of Cloud computing should pay attention to what you are consenting to. Even if you consent, realize that that consensus could be used as a means to access your private data you therefore have to take responsibility. Further realize that like all systems data protection is not impenetrable. Hackers are continuing to challenge these protective measures in place to protect your data and are successful in increasing scale.
In our current legal framework for the right to privacy as we know it there are extensive protection for data privacy but not in terms of its provision of suitable remedies. Normally courts would have the final say in evaluating whether privacy rights can be infringed. In the US even the courts as a line of defense has become a formality. In other jurisdictions such as South Africa we have published new legislation such as POPI although it is not implemented to its full potential and we have no gauge to see its success for internet based mobile uses it is potentially a step in the right direction.
Above all your privacy should firstly be your responsibility and then that of your service provider make sure you take steps to protect your information.
Footnotes:
[1] In June after I updated certain Apps I realised all my data – Photos, music, pdf files, research was missing. There was nothing wrong with my SD card.
[2] Universal Declaration of Human Rights, adopted and proclaimed by General Assembly resolution 217 A (III) of December 10, 1948.
[5] See Jonathan Burchell, The Legal Protection of Privacy in South Africa: A Transplantable Hybrid, vol. 13.1
ELECTRONIC JOURNAL OF COMPARATIVE LAW, (March 2009), http://www.ejcl.org/131/art131-2.pdf, page 3.
[6] Jonathan Burchell above page 19.
[7] See (http://www.theguardian.com/world/2014/sep/11/yahoo-nsa-lawsuit-documents-fine-user-data-refusal).
[8] See the article at <http://www.theguardian.com/law/2013/aug/31/microsoft-google-sue-us-fisa>.




another solid blog here. is it possible to cite more of your sources though? would like to know exactly where you got your info. anyway, very good stuff.
My pleasure. will add more citations shortly.
Thanks for a marvelous posting! I seriously enjoyed reading it,
you’re a great author.I will ensure that I bookmark
your blog and will come back in the future. I want
to encourage yourself to continue your great
posts, have a nice morning!
pleasure